Peta Documentation
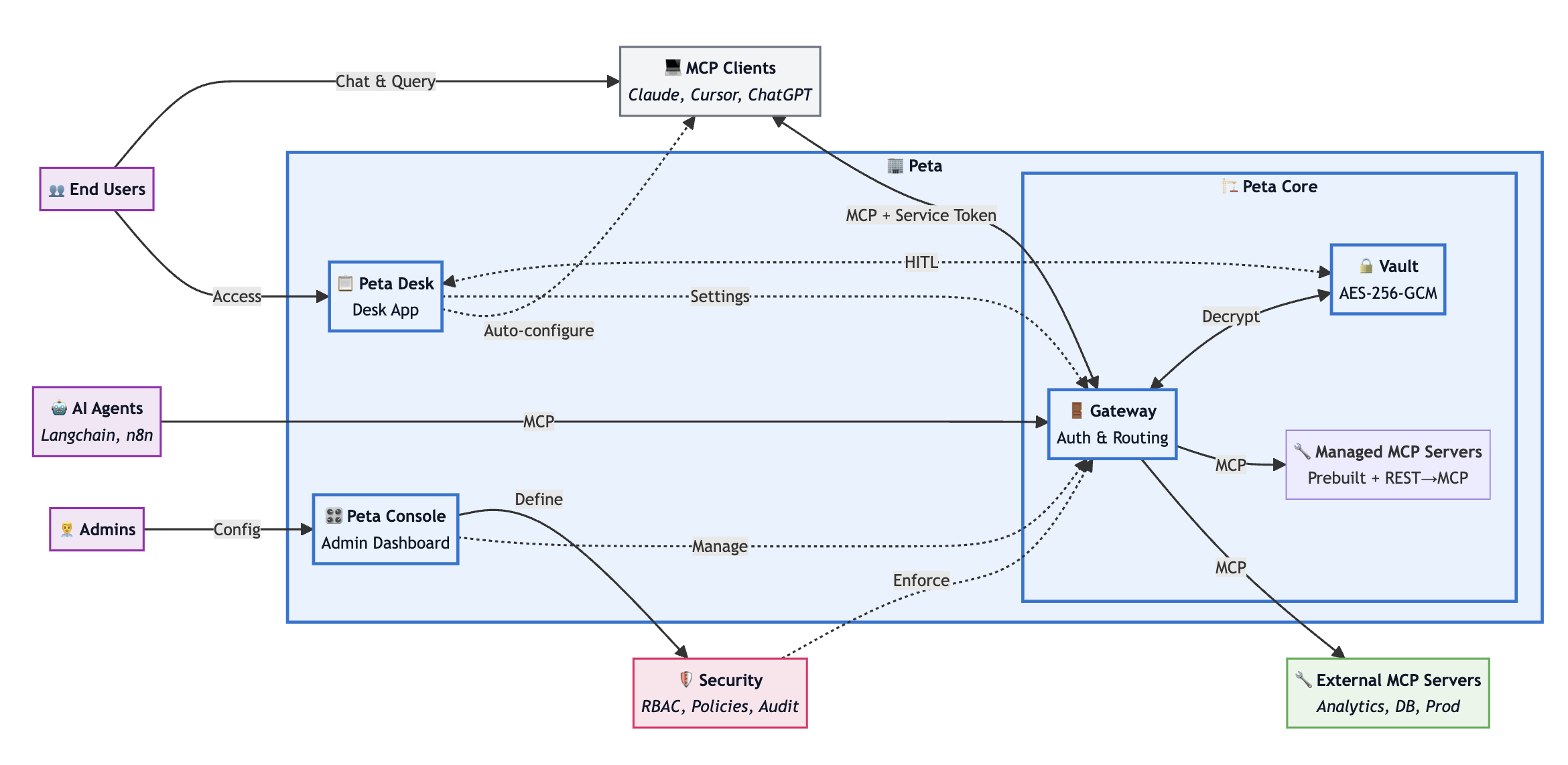
The Control Plane for MCP
Technical Overview
A single layer between your AI agents and your tools & APIs — policies enforced, credentials injected server-side, every call logged.
Platform Components
Peta consists of three components for MCP governance:
Peta Core
Managed MCP Runtime & Zero-Trust Gateway
Manages MCP server lifecycle, injects credentials server-side, and enforces policies at the gateway level.
Peta Console
Policy Engine & Access Control
Web-based administration interface for defining which users and agents can access which tools, with RBAC/ABAC policy configuration and usage monitoring.
Peta Desk
Human-in-the-Loop Approval System
Desktop app for real-time approval of high-risk operations, allowing you to review tool calls before execution with one-click approve/deny.
Project Links
Links to Peta resources and repositories:
- https://peta.io – product site
- https://docs.peta.io – documentation home
- https://github.com/dunialabs/peta-core – Peta Core repository
- https://github.com/dunialabs/peta-desk – Peta Desk repository
- https://dunialabs.io – Dunia Labs
MCP Transport Support in the Stack
Peta exposes HTTP/SSE to upstream clients and supports stdio, HTTP+SSE, and Streamable HTTP for downstream server integrations:
StdIO
Downstream process transport for local integrations and CLI tools
HTTP+SSE
HTTP with Server-Sent Events for real-time bi-directional communication over web protocols
Streamable HTTP
HTTP-based streaming for efficient large data transfer and progressive response handling
Three-Layer Security Architecture
Peta uses a three-layer security model to prevent credential exposure and maintain operational control.
Connection Layer
Authentication & Session Management
- AI agents authenticate using Peta service tokens (or use /mcp/public only when anonymousAccess=true, with per-source-IP per-minute rate limits)
- JWT signature and expiry validation
- Secure MCP sessions with operation tracking
Processing Layer
Request Validation & Execution
- RBAC/ABAC permission checks
- Just-in-time credential decryption (30s TTL)
- Tool execution with real credentials
- Sanitized response return
Control Layer
Policy Enforcement Mechanisms
- Multi-dimensional controls (operation type, data sensitivity)
- Rule-engine and policy DSL decisions
- Immutable audit trails
Technical Specifications
Protocol Compliance
MCP Protocol: 2025-11-25 specification (full compliance)
Encryption Standards
- AES-256-GCM at rest
- PBKDF2 (100,000+ iterations)
- Memory-only decryption with immediate cleanup
- Credential decryption TTL: 30 seconds
Enterprise Features
- SSO/SAML support for identity integration
- Tamper-evident, SIEM-ready logs
- SOC2 Type II ready, HIPAA capable, GDPR compliant
Platform Support
- Kubernetes 1.21+
- Docker containers
- AWS / GCP / Azure cloud platforms
- Air-gapped deployment support
Transport Modes
StdIO, HTTP+SSE, Streamable HTTP